Advanced Apple Debugging & Reverse Engineering, Chapter 31: DTrace
Por um escritor misterioso
Descrição
In this chapter, you'll use DTrace to hook objc_msgSend's entry probe and pull out the class name along with the Objective-C selector for that class. By the end of this chapter, you'll have LLDB generating a DTrace script which only generates tracing info for code implemented within the main executable that calls objc_msgSend.

Advanced Apple Debugging & Reverse Engineering, Chapter 31: DTrace vs. objc_msgSend

Evolution of the Unix System Architecture: An Exploratory Case Study

Securing Your Fleet
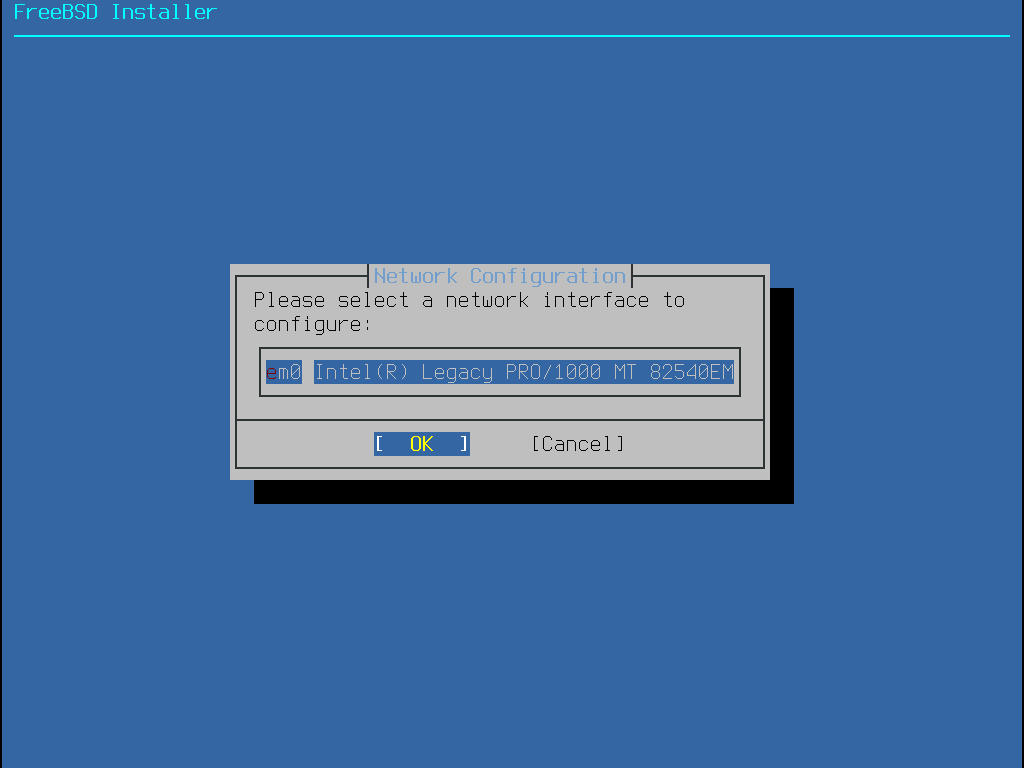
FreeBSD Handbook FreeBSD Documentation Portal

Franklin Byaruhanga (@byaruhaf) / X
XNU: a security evaluation D Keuper - Reverse Engineering Mac OS X
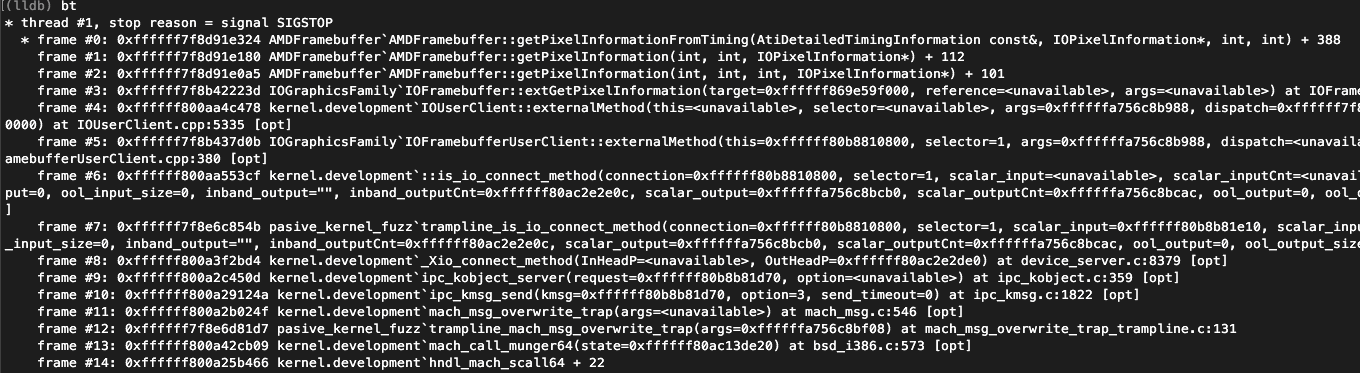
Virus Bulletin :: VB2019 paper: Play fuzzing machine – hunting iOS/macOS kernel vulnerabilities automatically and smartly

Advanced Apple Debugging & Reverse Engineering, Chapter 1: Getting Started
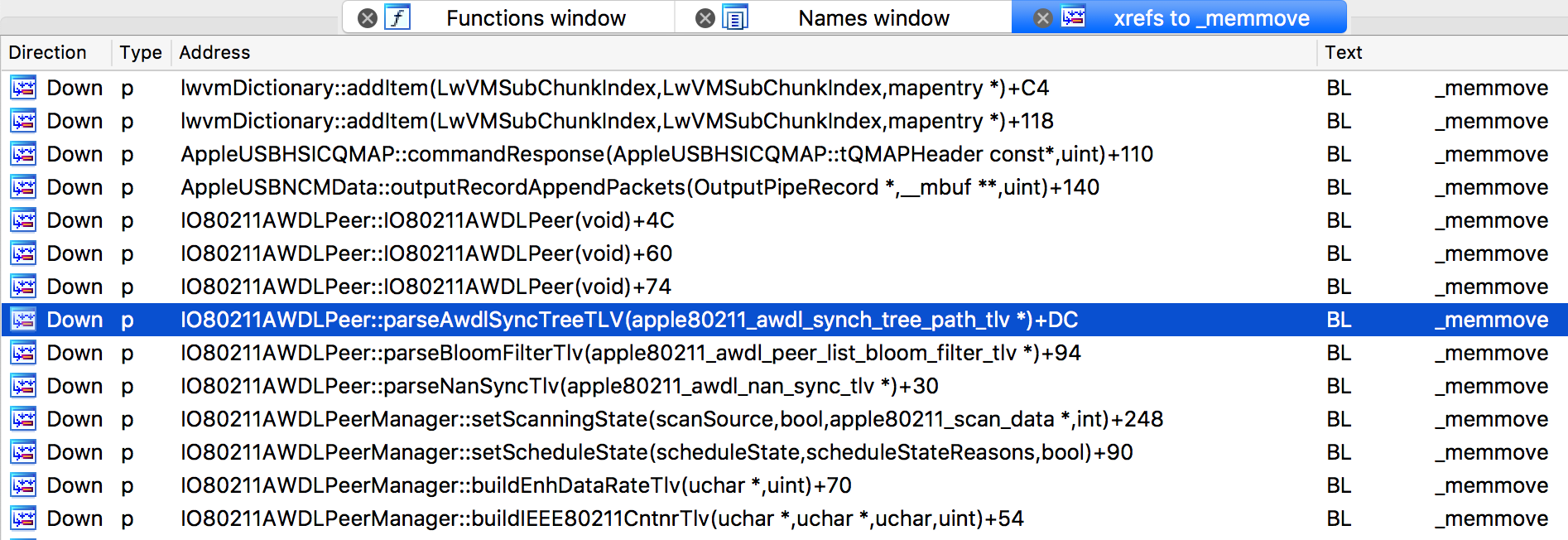
Project Zero: An iOS zero-click radio proximity exploit odyssey
de
por adulto (o preço varia de acordo com o tamanho do grupo)






