Thoughts on the Application of Low-Interactive Honeypot Based on Raspberry Pi in Public Security Actual Combat, LIHRP
Por um escritor misterioso
Descrição

Low, Medium and High Interaction Honeypot Security

Learning cyberattack patterns with active honeypots

Thoughts on the Application of Low-Interactive Honeypot Based on Raspberry Pi in Public Security Actual Combat, LIHRP
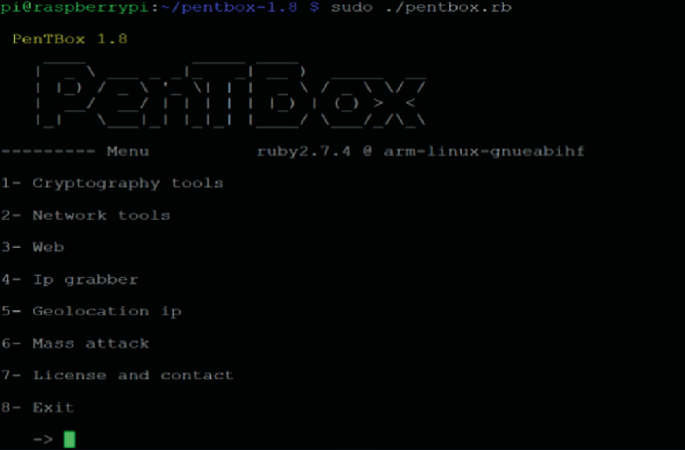
Thoughts on the Application of Low-Interactive Honeypot Based on Raspberry Pi in Public Security Actual Combat, LIHRP

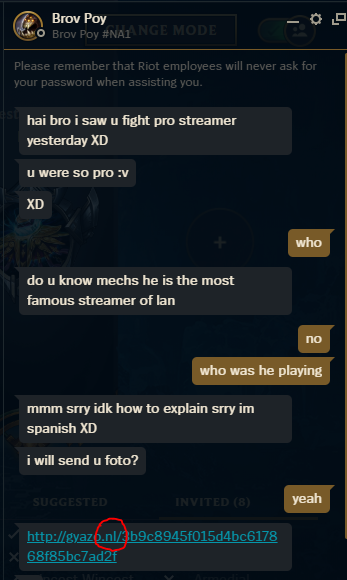
Testing a Low-Interaction Honeypot against Live Cyber Attackers

I SETUP A HONEYPOT AND GOT MORE THAN 3K SSH SESSIONS FROM HACKERS #threatanalysis #raspberrypi

Testing a Low-Interaction Honeypot against Live Cyber Attackers

Low Interaction Honeypot - an overview

Testing a Low-Interaction Honeypot against Live Cyber Attackers

PDF] Rethinking the Honeypot for Cyber-Physical Systems
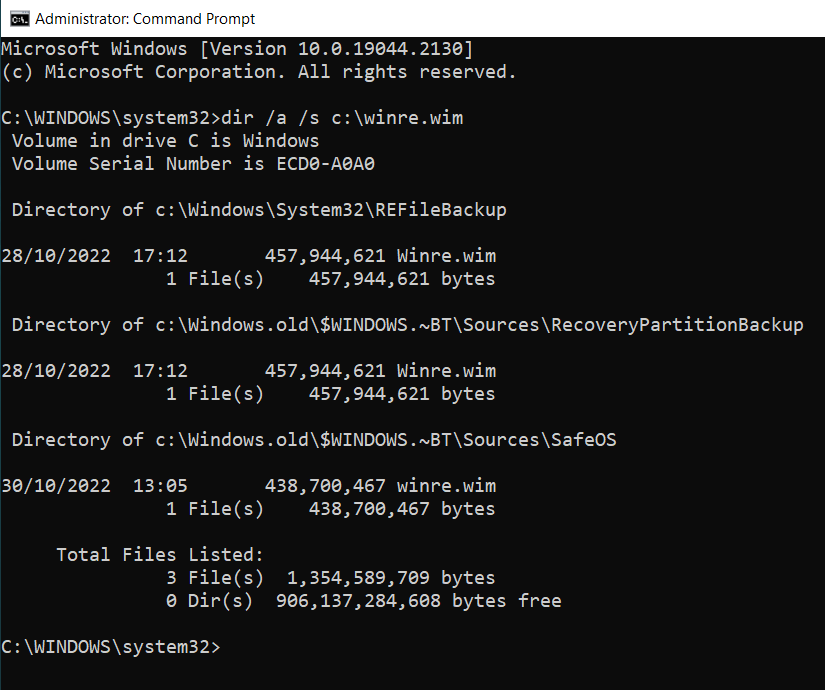
Step by Step Guide on setting up SMB, RDP, SSH and HTTP HoneyPot in Raspberry Pi, by Elaine Hung
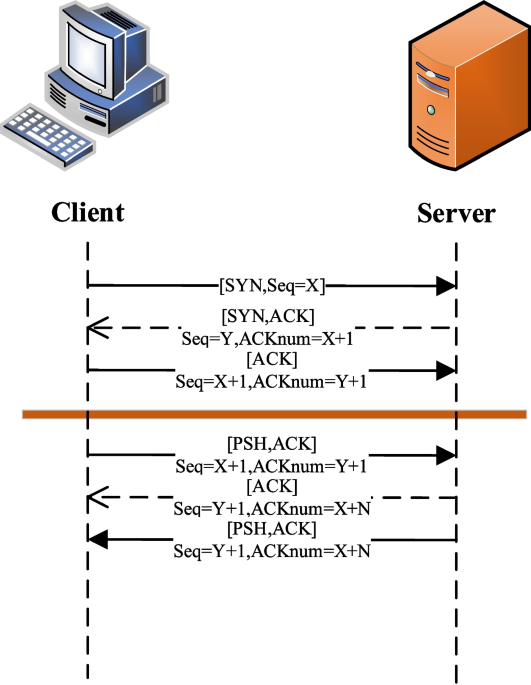
A new dynamic security defense system based on TCP_REPAIR and deep learning, Journal of Cloud Computing
de
por adulto (o preço varia de acordo com o tamanho do grupo)