Port Scan in Ethical Hacking - GeeksforGeeks
Por um escritor misterioso
Descrição
A Computer Science portal for geeks. It contains well written, well thought and well explained computer science and programming articles, quizzes and practice/competitive programming/company interview Questions.
A Quick Guide To Network Scanning for Ethical Hacking
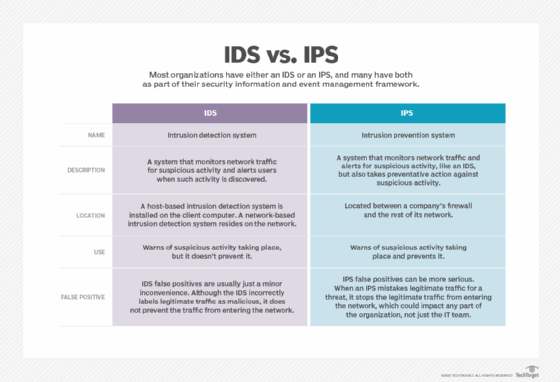
What is Snort and how does it work?
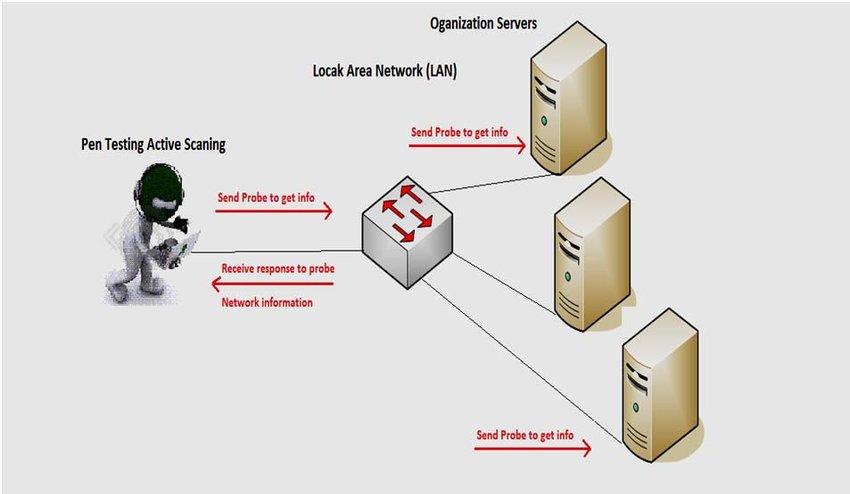
Network Scanning in Ethical Hacking

CSE CBCS Syllabus by Karunya Institute of Technology and Sciences

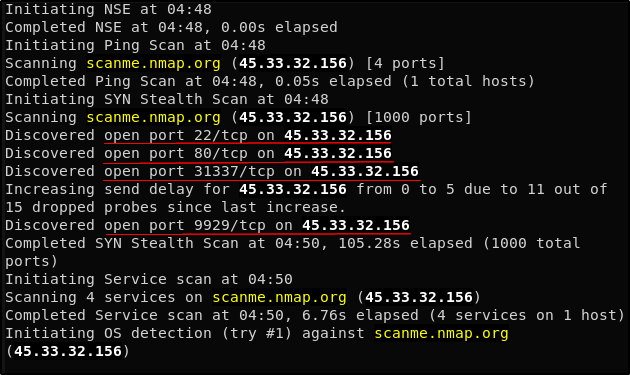
Top 8 Nmap Commands you should know in 2024 - Great Learning

What is footprinting? Understanding the Steps of Footprinting
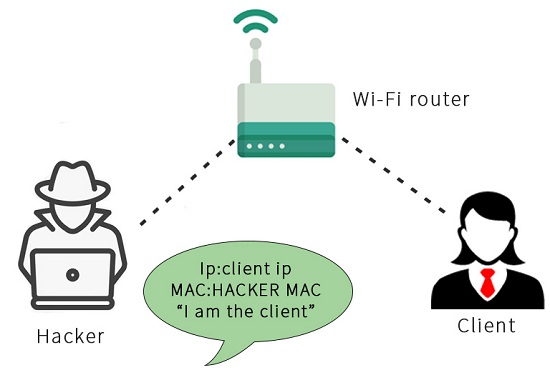
MITM Attacks Man-in-the-Middle Attacks - javatpoint

Exploit Development-Everything You Need to Know « Null Byte

Certified Ethical Hacker (Practical):Journey to gateway to Ethical
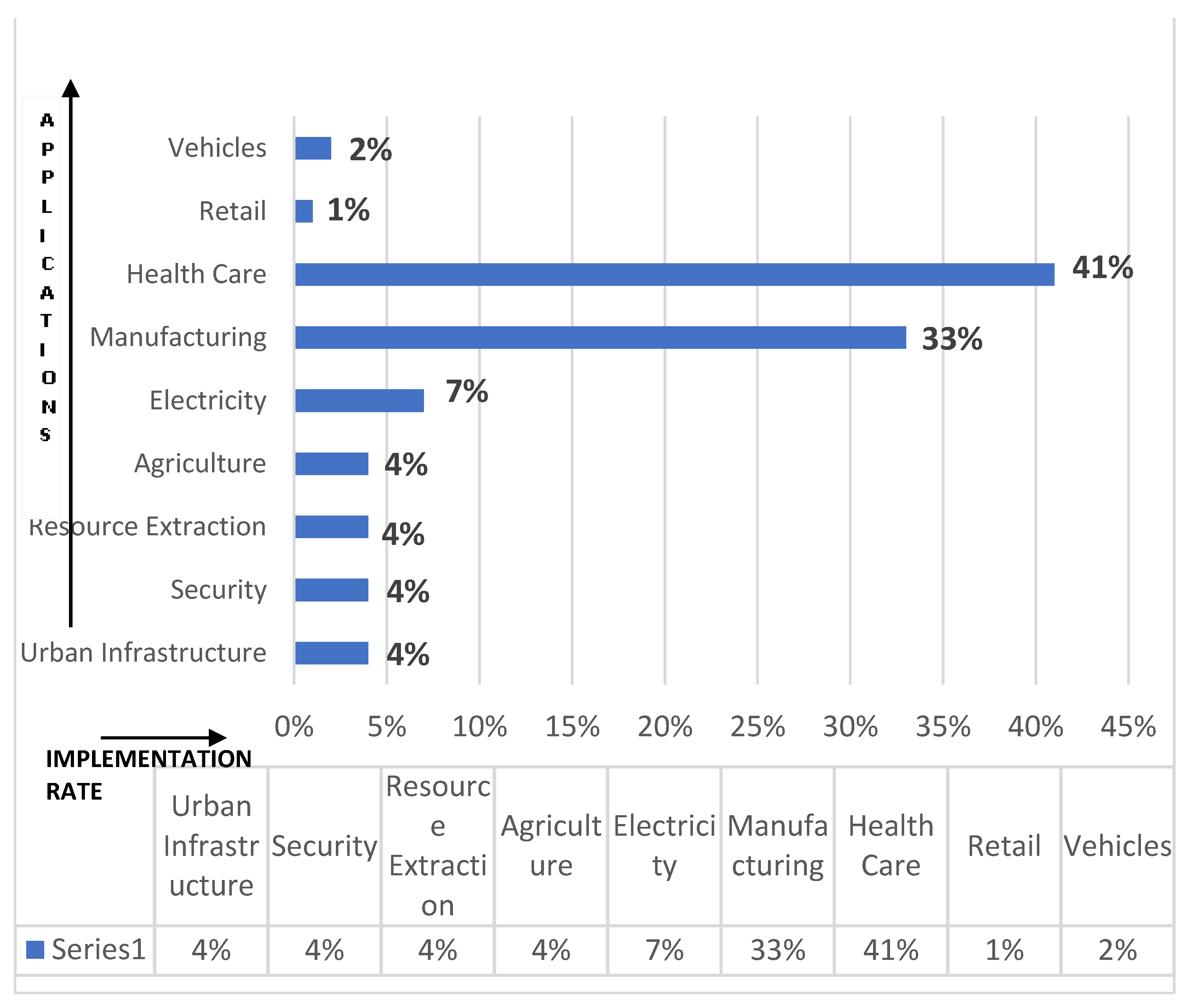
Sensors, Free Full-Text

Port Scanning Techniques By Using Nmap - GeeksforGeeks

Explore The 5 Phases of Ethical Hacking: Webinar Wrap-Up

Week 4 Solution, PDF, Transmission Control Protocol
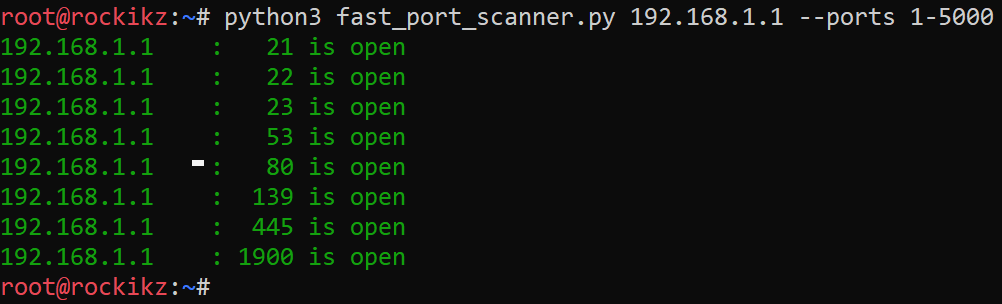
How to Make a Port Scanner in Python - The Python Code
de
por adulto (o preço varia de acordo com o tamanho do grupo)