Hack Like a Pro: How to Hack the Shellshock Vulnerability « Null
Por um escritor misterioso
Descrição

Message Authentication and Provenance Verification for Industrial Control Systems

Hack Like a Pro: How to Hack the Shellshock Vulnerability « Null Byte :: WonderHowTo

What is Shellshock? This infographic explains how a Shellshock attack works and how to stay safe – Sophos News
TryHackMe Advent of Cyber 2 [2020]

Processing tweets for cybersecurity threat awareness - ScienceDirect
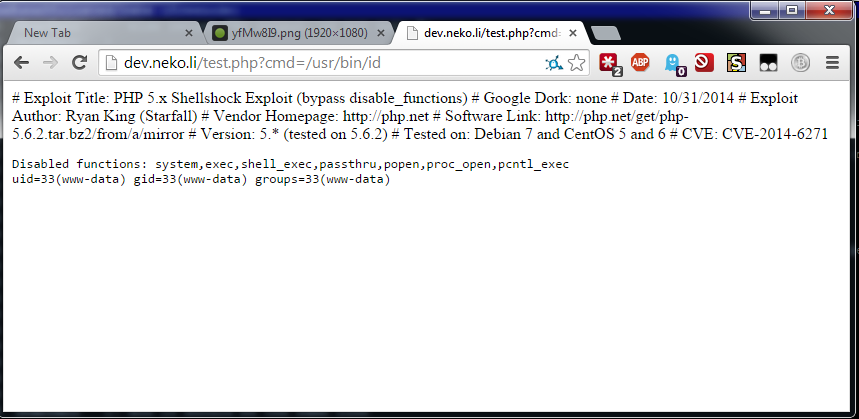
PHP < 5.6.2 - 'Shellshock' Safe Mode / disable_functions Bypass / Command Injection - PHP webapps Exploit

Processing tweets for cybersecurity threat awareness - ScienceDirect
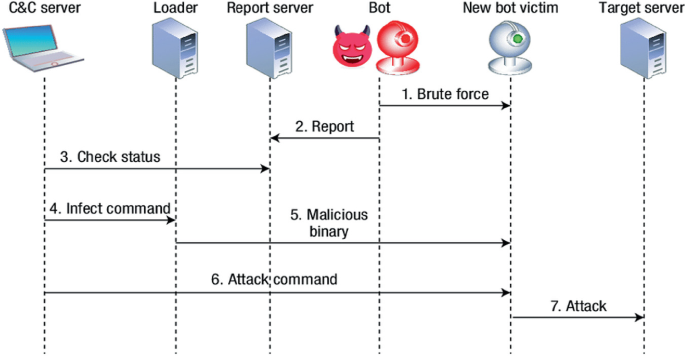
Determining Vulnerabilities of Pervasive IoT Devices and Their Geographic Distribution

Keep Calm and Hack The Box - Shocker

Shellshock Vulnerability and Attack

Inside Shellshock: How hackers are using it to exploit systems
de
por adulto (o preço varia de acordo com o tamanho do grupo)